You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
For decades, passwords have been the backbone of digital security. From email accounts and bank logins to work systems and social media profiles, a simple combination of letters, numbers, and symbols has stood between users and their digital lives. Yet despite constant reminders to create “strong” passwords, the system is breaking down.
People forget passwords. They reuse them. They write them down. Hackers steal them. Entire industries have formed around managing, resetting, and recovering lost credentials. As cyber threats grow more sophisticated and digital dependence deepens, passwords are proving inadequate for a world that demands both security and convenience.
In response, a quiet revolution is underway. Biometrics—authentication based on who you are rather than what you remember—are rapidly replacing passwords across devices, apps, and services. This shift marks one of the most significant changes in digital security since the internet went mainstream.
Passwords were never designed for the modern digital ecosystem.
The average user manages dozens of accounts. Expecting people to remember unique, complex passwords for each one is unrealistic. As a result, users:
Reuse passwords across platforms
Choose predictable patterns
Rely on insecure storage methods
These behaviors create vulnerabilities that attackers exploit easily.
Passwords can be compromised through:
Phishing emails and fake websites
Data breaches
Malware and keyloggers
Social engineering attacks
Once stolen, a password can be reused instantly, often without detection.
Security guidelines demand longer passwords with mixed characters, frequent changes, and no reuse. While well-intentioned, these rules often make security worse by encouraging unsafe coping behaviors.
Passwords don’t just fail users—they burden systems.
Password resets and account recovery consume significant resources. Help desks, IT teams, and security operations spend enormous time handling credential-related issues.
Complex login processes frustrate users, leading to:
Abandoned sign-ups
Reduced engagement
Lost revenue
Convenience is now a competitive advantage, not a luxury.
Many password rules give an illusion of security while failing to stop real threats. Attackers adapt faster than static rules can keep up.
Biometrics authenticate identity using physical or behavioral traits.
These include:
Fingerprints
Facial features
Iris and retina patterns
Hand geometry
They rely on traits that are difficult to replicate or steal remotely.
Behavioral systems analyze patterns such as:
Typing rhythm
Touch pressure
Gait and movement
Voice characteristics
These add an extra layer of continuous authentication.
Several forces are driving biometric adoption simultaneously.
Biometrics remove the need to remember anything. A glance, a touch, or a voice command replaces complex credentials, making secure access nearly effortless.
Modern smartphones, laptops, and wearables ship with biometric sensors built in. Adoption does not require new habits—only activation.
Biometric data cannot be guessed, phished, or brute-forced in the traditional sense, closing off many common attack vectors.
Biometrics change the threat landscape.
Unlike passwords, biometric traits are inherently unique, making large-scale credential theft far more difficult.
Many biometric systems store data locally on devices rather than central servers, reducing breach risk.
Biometrics are often combined with device possession and behavioral signals, creating layered security without extra effort from users.
Biometrics are part of a broader move toward passwordless systems.
Instead of one static secret, systems evaluate:
Device integrity
Location consistency
Behavioral patterns
Biometric confirmation
Access becomes a decision, not a challenge-response.
Passwordless systems allow users to move between devices without re-entering credentials repeatedly.
Removing passwords eliminates one of the most common entry points for cybercrime.
Despite advantages, biometrics raise serious questions.
Unlike passwords, biometric traits cannot be reset if compromised. This makes secure storage and handling critical.
Biometrics can be associated with tracking, monitoring, and misuse if improperly regulated or centralized.
Users often activate biometrics without fully understanding how data is stored, processed, or shared.
The industry is responding to privacy concerns.
Biometric data is increasingly stored in secure hardware environments, never leaving the device.
Systems store encrypted templates, not raw images, making reconstruction extremely difficult.
Most platforms allow users to disable biometrics or combine them with other authentication methods.
Biometrics are expanding beyond personal devices.
Biometric authentication reduces fraud while simplifying transactions, especially in mobile banking.
Offices are replacing access cards and passwords with biometric entry systems for physical and digital access.
Biometrics help ensure only authorized individuals access medical records, reducing identity-related errors.
Biometrics are not a universal solution.
Poor lighting, injuries, or noise can affect biometric accuracy.
Not all users can reliably use biometric systems due to physical or medical conditions.
No system is perfect. Balancing security and usability remains a challenge.
AI is accelerating biometric evolution.
Machine learning models continuously refine recognition accuracy over time.
AI adjusts security requirements dynamically based on perceived risk.
Behavioral AI can detect anomalies even after authentication, stopping attacks mid-session.
The move away from passwords changes user expectations.
Authentication happens naturally, reducing friction without reducing protection.
Users protect devices more carefully because identity is tied to possession.
Understanding how identity systems work becomes part of digital literacy.
Biometrics may not be the final step.
Future systems may authenticate based on environment, behavior, and intent simultaneously.
Instead of logging in once, identity may be verified continuously in the background.
Access decisions may evolve moment by moment, not session by session.
Passwords are unlikely to vanish overnight.
Legacy systems and backup access methods will continue using passwords for years.
They may remain as fallback mechanisms rather than primary defenses.
Changing security habits takes time, trust, and consistent performance.
Authentication shapes power and control.
As biometrics spread, ownership and governance of identity data become critical questions.
Systems must ensure that biometric adoption does not exclude vulnerable populations.
Without trust, even the most secure technology will fail adoption.
The decline of passwords is not a technological trend—it is a necessity born from scale, risk, and human limitation. Biometrics rise not because they are perfect, but because they align better with how people actually live, work, and interact with technology.
As authentication shifts from memory-based secrets to identity-based signals, security becomes more personal, more seamless, and more complex. The challenge ahead is not simply replacing passwords, but ensuring that the systems built to replace them respect privacy, preserve choice, and remain worthy of trust.
The future of authentication is not about remembering who you claim to be. It is about proving who you are—quietly, securely, and without friction.
Disclaimer:
This article is for informational purposes only. Authentication technologies, security practices, and privacy regulations vary by region and continue to evolve.






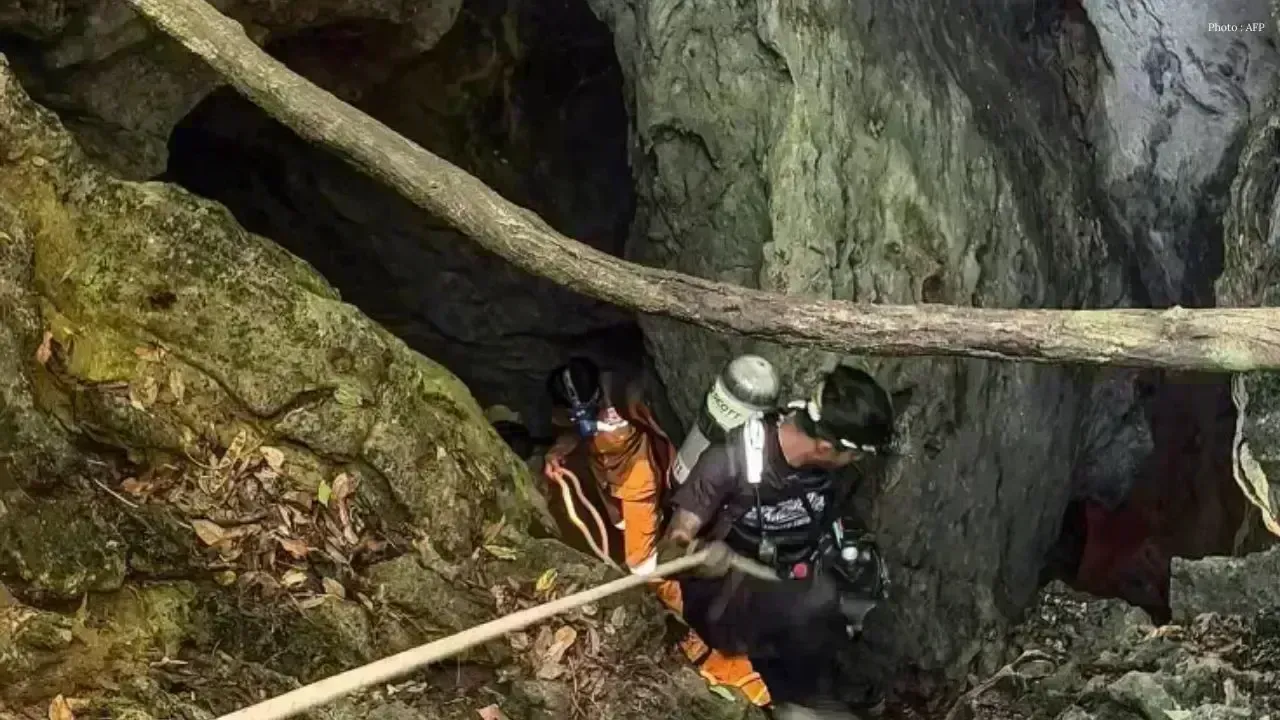



Nine Injured After GOF Chase Crash in Jeli
Police arrest suspected migrant smuggler after high-speed chase ends in crash involving undocumented
Singapore Urges North Korea to Keep Dialogue
Singapore calls on North Korea to join regional talks and maintain diplomatic communication amid ris

Scha Alyahya Hails New Era of Malaysian Cinema
Malaysian actress Scha Alyahya says local entertainment is reaching new creative heights with strong

Selangor Pig Farm Shutdown Nears Completion
Selangor enters final phase of closing pig farms in Tanjong Sepat with 11,000 animals remaining befo

India Rejects China-Pak Kashmir Remarks
India strongly opposes China-Pakistan references to Jammu and Kashmir, calling them violations of so

Taiwan Conflict May Trigger Nuclear Crisis
A new global security study warns that any US-China conflict over Taiwan could escalate into a dange