You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
Biometric data, including facial scans, fingerprints, and voice patterns, was once primarily associated with secure environments. Now, it's a staple of daily life. From smartphones that recognize our features to apps requiring our biology for authentication, biometrics are deeply embedded in modern systems.
As industries ramp up their biometric adoption, concerns grow regarding aspects such as data storage, user consent, portability, and potential misuse. Unlike passwords, biometric traits such as faces and fingerprints can't be reset. The rise of advanced AI technologies complicates the risk landscape further, raising the stakes for user security.
Consequently, biometric privacy transcends a mere technical matter—it's fundamentally about personal safety. Users are urged to proactively grasp the implications of their biometric data collection, storage, and potential exposure.
Most associate biometrics with fingerprints and facial recognition. However, today's systems collect a broader array of identifiers, including:
facial geometry and micro-expressions
fingerprints and palm-prints
retina and iris patterns
voice patterns and tone signatures
gait patterns and posture
typing rhythm and touchscreen behavior
vein patterns
ear shape
heart-rate signatures from wearables
With the ability to detect intricate identity aspects, maintaining privacy has become even more paramount.
The sensitivity of biometric data arises from several factors:
If compromised, biometric data cannot be altered like passwords.
Biometrics can permanently link identity to actions, behaviors, and locations.
Biometric traits may be collected unintentionally through surveillance.
Advancements in AI can facilitate identity theft through voice synthesis or deepfakes.
Biometric tracking may cross various systems and devices.
As such, biometric privacy should be regarded with the same importance as financial or medical information.
To enhance your biometric privacy in daily life, consider these practical actions:
Excessive sharing increases risk. Avoid submitting biometric data unnecessarily:
Enable facial recognition only in essential applications.
Opt for traditional password verification where possible.
Reject unnecessary biometric prompts on websites.
Avoid sharing voice data or videos unless absolutely necessary.
Assess whether platforms truly require your biometric information or just convenience.
Always select the least invasive method available.
While biometric features enhance convenience on phones and devices, manage settings judiciously:
Disable features like face unlock, using strong passcodes instead.
Turn off fingerprint unlock when not needed.
Deactivate voice-assistant wake commands that analyze speech continuously.
Disable emotion-analysis or attention-tracking features.
Limit gestural recognition capabilities when not in use.
This strategy minimizes continual biometric scrutiny by devices.
Applications often request camera and microphone access without genuine need. Monthly permission checks are advisable:
Revoke camera permissions from apps that don't require access.
Remove microphone access from apps that don't use it for calls.
Limit background activities of sensor-using apps.
Stop permissions for apps that inappropriately track behavior.
Constant monitoring is crucial to prevent silent data collection.
While fun, popular filters utilize face mapping extensively, gathering intricate data such as:
detailed facial geometry
emotional expressions
eye movement
smile dynamics
jaw structure
This data can extend beyond entertainment purposes. Limit use of such apps and avoid those needing multiple facial angles for 3D modeling.
Voice biometrics are prevalent in secure sectors, but voice cloning risks threaten security:
Opt for numeric codes rather than voice verification
Avoid voiceprint registration when possible.
Many platforms permit users to eliminate biometrics. Regularly:
Remove unused biometric data from old applications.
Request identity-verification services to erase records.
Relying on biometrics as a backup for subpar passwords is risky. Instead:
Create complex passphrases.
Employ multi-factor authentication.
Wearables capture sensitive metrics such as heart rates and movement patterns. Consider these for privacy:
Deactivate continuous heart rate monitoring.
Limit unnecessary syncing with third-party applications.
Modern environments use facial recognition across various settings. To mitigate this:
Try not to gaze directly at security cameras if possible.
Wear hats or sunglasses in high-traffic surveillance areas.
Avoid sharing detailed facial photos. Consider these precautions:
Don’t send selfies to unfamiliar contacts.
Avoid uploading high-def images to unsecured platforms.
Protecting children from biometric risks is critical. Guidelines include:
Refrain from enrolling kids in biometric ID systems.
Users can often choose between on-device storage and cloud options. Best practices include:
Opt for local storage of biometric keys whenever possible.
Steer clear of services requiring cloud submissions.
Before sharing biometric data, inquire about:
Storage processes
Behaviors like scrolling and typing can also serve as biometrics. Manage exposure through:
Limit behavioral tracking.
Many AI applications can create detailed models based on images. Limit uploads and participation:
Avoid sharing whole videos or extensive audio clips.
Biometric data is fundamental to individual identity. Its misuse can have serious implications. Users need to treat biometric information with the same diligence as other crucial identity markers.
As biometric systems become ingrained in everyday life, users must safeguard their digital identity. Protecting this data isn't just about paranoia—it's about securing irreplaceable aspects of personal identity. Awareness, strict controls on data sharing, and judicious engagement with technology can empower users to regain control of their biometric privacy.
This article serves as guidance on biometric privacy. For tailored advice, consult cybersecurity professionals.










V-Mart Shoplifting Clip Raises Serious Security Concerns
Viral video from V-Mart store shows unusual shoplifting method, raising concerns over rising theft c
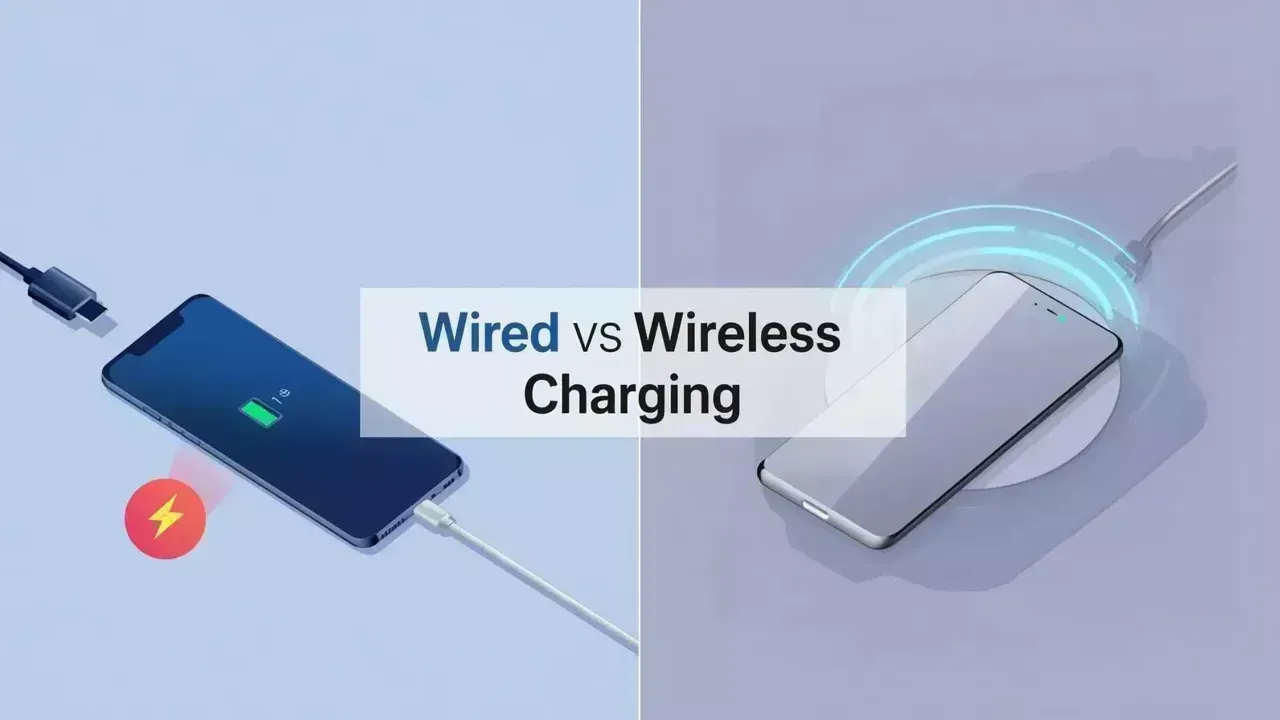
Wired vs Wireless Charging: A Comparison for Speed and Battery Longevity
Explore the differences between wired and wireless charging regarding speed and battery health in th

High-Speed Chase Ends in Crash in California
Police chase across Riverside and San Bernardino ends in crash after Grappler device used; armed sus

China Weighs Role in Iran Ceasefire Talks
China evaluates its diplomatic role in Iran ceasefire as Trump prepares Beijing visit, balancing ene

Made a Mistake While Sending an Email? Quick Fixes to Resend or Recall It
Accidentally sent the wrong email? Explore effective methods to unsend or correct your emails swiftl
China K-Pop Ban Continues Amid Cultural Tensions
China’s unofficial ban on K-pop persists for nearly a decade, driven by geopolitical tensions, cultu