You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!
Post by : Samjeet Ariff
With the rapid changes in our work culture, being tethered to a specific device or site is increasingly obsolete. Whether you find yourself traveling, home-based, or needing to swiftly manage tasks on the move, remote access to your files has become crucial. However, this convenience should not compromise security. Many users adopt remote tools without fully comprehending the associated risks, leaving sensitive information exposed. Fortunately, with the correct configuration, you can achieve secure remote access to your laptop files while safeguarding your data.
Remote access enables you to connect to your laptop from another device—be it a smartphone, tablet, or another computer—and operate it as if you were right there. This capability allows you to open documents, run applications, and manage tasks from virtually anywhere.
In today’s adaptive work landscape, the ability to work remotely is essential. If you happen to leave a critical file at home or need to finalize a presentation while away, remote connectivity guarantees that you remain in touch with your responsibilities.
A highly effective way to access your laptop from another device is utilizing remote desktop applications. Tools such as Chrome Remote Desktop and Microsoft Remote Desktop are among the popular choices.
These platforms allow comprehensive access—not limited to files alone—making them well-suited for professionals requiring full operational capability. Upon connection, you can manipulate your laptop just like you would in person.
For those who don't require complete control over the system, cloud storage presents a straightforward alternative. Solutions like Google Drive and Dropbox enable file upload and access anytime.
This option especially benefits documents, images, and minor projects. Additionally, it offers a backup layer, shielding your files even if your primary device is out of commission.
File syncing applications automatically synchronize files across devices. Thus, any modifications on your laptop will instantly reflect on other connected devices.
Such methods are ideal for users who operate on multiple devices and demand real-time file updates without manual interference. This not only saves time but minimizes the risk of utilizing outdated documents.
Establishing remote access is more straightforward than most realize. Begin by installing a trusted remote access application on your laptop and logging in with your account. Following this, enable remote connectivity and create a robust password or PIN.
Next, install the corresponding app on the device you intend to use for the connection. Once both gadgets are linked, secure laptop access becomes feasible at any time. This uncomplicated setup ensures safe remote desktop access without complex configurations.
Despite the advantages of remote access, improper handling can lead to vulnerabilities. Potential threats include unauthorized access, weak passwords, and unsecured networks, all endangering your data.
Utilizing public Wi-Fi without adequate security measures stands as a significant blunder. Cybercriminals can intercept data, risking sensitive material exposure. Acknowledging these threats is paramount in fortifying your system's protection.
Always implement a robust password for remote access that is not easily guessed. Adding two-factor authentication (2FA) provides an additional layer of security through a secondary verification requirement.
Public networks often lack security. Should you need to use them, consider employing a VPN (Virtual Private Network) to encrypt connections and safeguard your data.
Obsolete applications can harbor security flaws. Regular updates ensure your system receives the latest security fixes, thereby lessening potential threats.
Failing to log out can open your system to vulnerabilities. Always ensure you log out after utilizing remote access, particularly on shared or public devices.
The choice between remote desktop solutions and cloud storage hinges on specific requirements. If extensive access to your laptop, including software and configurations, is essential, remote desktop applications may be preferable. Conversely, if only file access is needed, cloud storage offers a quicker and simpler approach.
Comprehending this distinction can assist in selecting the most efficient and secure file access solution according to your circumstances.
As remote work gains traction, security concerns rise to the forefront. Accessing files from various locations increases the chance of data exposure if not adequately managed.
By adhering to safe practices, you can harness the advantages of remote work while keeping your data secure. A security-first strategy for remote working cultivates long-term safety and peace of mind.
Remote access is an empowering tool that offers both flexibility and independence. However, this liberty carries with it responsibilities. Establishing the appropriate tools and adhering to fundamental security practices can facilitate work from any location without compromising safety.
In our digitally driven age, the goal transcends mere convenience—it’s about achieving safe and effective remote work. Striking the right balance among both factors promotes a system that genuinely enhances your productivity.
This article serves only as an informational resource, providing general insights on remote access tools and security practices. Users should verify software settings, security features, and network safety prior to enabling remote access. Individual configurations may differ based on devices, operating systems, and use. Always adhere to official protocols and cybersecurity best practices to safeguard your data.










Japan Wildfire Forces Mass Evacuation in Iwate
Massive forest fire in Iwate spreads fast, forcing evacuation of over 1,000 residents as teams battl

Malaysia Cup Final Ticket Prices Stay Same
MFL keeps ticket prices unchanged for JDT vs Kuching City final despite rising costs, ensuring affor
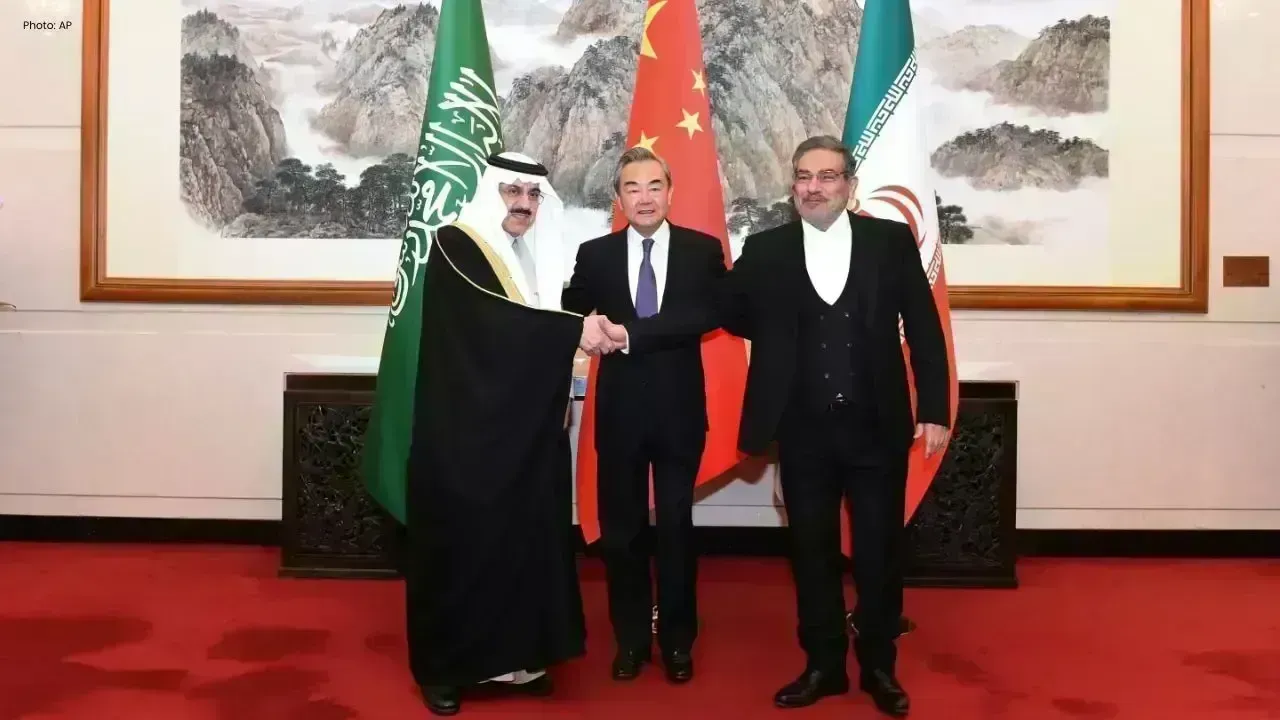
China's Subtle Shift in Iran Conflict Diplomacy
As global tensions rise, China quietly enhances its role in Iran diplomacy, emphasizing stable energ

Kuwait Continues Remote Learning, Exams Online
Kuwait keeps remote learning and online exams, while coast guard allows daytime sailing and authorit

Bhutan-India Car Smuggling Probe Intensifies
Bhutan customs team in Kerala to probe cross-border vehicle smuggling under Operation Numkhor, invol

Nepal Protests Erupt Over Border Customs Rule
Strict customs enforcement on India goods sparks protests in Nepal, raising prices and disrupting da