You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!
Post by : Samjeet Ariff
In our increasingly online world, a password serves as the primary shield for your personal information, financial accounts, and social media profiles. However, countless individuals still opt for weak or easily guessable passwords, allowing hackers to infiltrate their accounts—often within mere minutes.
By understanding the tactics hackers use to crack passwords, you can better safeguard your digital presence.
Many users default to passwords like names, birthdays, or popular combinations such as “123456” and “password.” These passwords are incredibly easy for cybercriminals to guess using automated tools.
Hackers rely on vast databases of common passwords to execute rapid-fire combinations. If your password is weak or widely used, expect it to be breached in no time.
Additions like “Password123” don’t significantly enhance security either, as these patterns are familiar to attackers.
A prevalent hacking technique is the brute force attack, in which software automatically churns through thousands or even millions of password combinations in seconds.
Modern systems can quickly assess countless combinations, especially with shorter passwords. An uncomplicated or brief password may be cracked in moments.
Opting for longer and more complex passwords greatly extends the time needed for cracking, rendering brute force tactics less effective.
Not every hacker employs technical means; many resort to phishing, luring users into revealing their passwords.
You may receive a deceitful email or message appearing to be from a trusted source like Gmail or Facebook, prompting you to log in or verify your details.
Such counterfeit sites look legitimate, but once your password is entered, it is sent straight to the hacker.
This approach is particularly dangerous as it sidesteps technical defenses by preying on human behavior.
Major data breaches expose vast amounts of usernames and passwords from various sites and applications. Cybercriminals gather this information to access accounts across multiple platforms.
Reusing passwords across different platforms amplifies the risk; one breach can jeopardize all accounts.
This emphasizes the importance of unique passwords for every account to ensure safety.
Malicious software, often installed unknowingly, can log every keystroke. This includes sensitive information like passwords and messages.
Once keyloggers are set up, they transmit your data to hackers invisibly. Clicking unknown links or downloading files from unreliable sources heightens this risk.
Maintaining a secure system and avoiding dubious downloads is critical in preventing these threats.
Your foremost defense against cyber threats is a robust password. An ideal password should be:
Avoid utilizing any personal information like names or dates.
A password manager can simplify the process of generating and securely storing complex passwords, sparing you from having to memorize them all.
Even if someone acquires your password, two-factor authentication (2FA) provides an additional security layer requiring a secondary verification, such as a code sent to your device.
Most major online services provide this feature; activating it can significantly lower the risk of unauthorized entries.
It functions as a powerful backup defense, complicating attempts by hackers to compromise your accounts.
Sometimes, your account might exhibit indications of a breach. Look out for:
If you observe any of these signs, modify your password immediately and secure your account.
Cyber risks are constantly evolving, and hackers are becoming increasingly sophisticated. Relying on weak passwords and outdated practices can expose your personal and financial information to significant risk.
Implementing straightforward measures like forming strong passwords, activating added security, and remaining vigilant against threats can keep you protected from potential cyber-attacks.
This article is intended for informational purposes only, aiming to inform readers about cybersecurity strategies. Always adhere to official security guidelines provided by the platforms you utilize.









Strike Hits Tyre Amid Israel Evacuation Warning
Airstrike hits Tyre after Israeli warning to evacuate, escalating tensions in southern Lebanon despi

Israeli Strike Kills Al Jazeera Journalist Gaza
Al Jazeera journalist Mohammed Wishah killed in Israeli drone strike in Gaza, raising concerns over

North Korea Tests New Weapons Amid Global Tensions
North Korea tests advanced weapons including EM systems and missiles as global focus shifts to Middl

Thai Army Builds Shelters Along Cambodia Border
Royal Thai Army accelerates construction of 182 bomb shelters along Thai-Cambodian border to strengt

Nepali Man Confronts Tourists Over Gutka Spit
Nepali man making Indian tourists clean gutka spit, sparking debate on civic sense, responsible tour
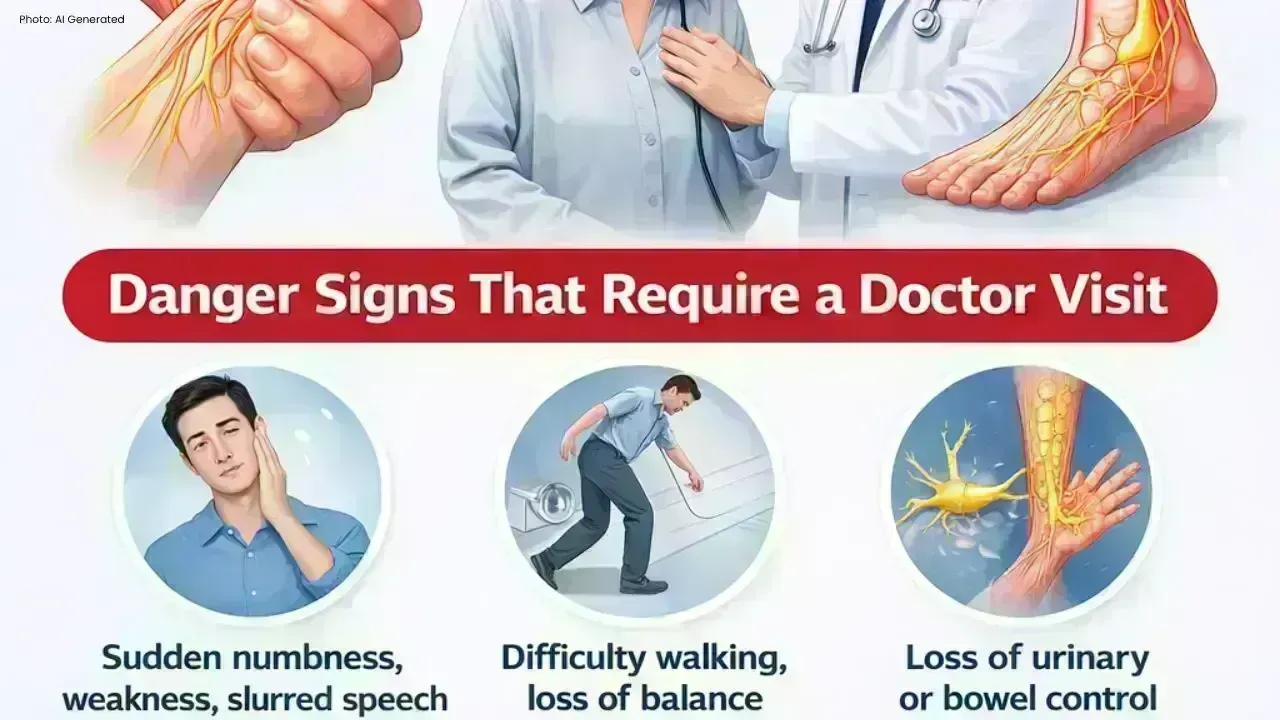
Numbness Warning Linked to Serious Diseases
Thailand’s Ministry confirms numbness in hands and feet can signal serious illness and urges people